Can an Intrusion Alarm Integrate with Existing CCTV and Access Control Systems?
In an era where physical and digital security threats evolve at breakneck speed, organizations can no longer rely on fragmented, siloed security measures. Facility managers, IT directors, and security professionals often find themselves asking a critical question: Can an intrusion alarm integrate with existing CCTV and access control systems?
The definitive answer is a resounding yes. Not only is it possible to integrate your intrusion alarm with your existing video surveillance and access platforms, but doing so has become the gold standard for modern, enterprise-level security architecture. By converging these previously distinct technologies into a unified ecosystem, businesses can transition from a reactive security posture to a highly proactive, intelligent defense strategy.
This comprehensive guide delves deep into the mechanics, benefits, technological protocols, and expert insights surrounding the integration of an intrusion alarm with closed-circuit television (CCTV) and automated access control frameworks. Whether you are safeguarding a sprawling corporate campus, a high-security industrial facility, or a multi-tenant commercial building, understanding this technological synergy is vital.
The Core Foundation: Understanding the Modern Intrusion Alarm
Before exploring the complexities of system integration, we must define the cornerstone of physical security: the intrusion alarm. Traditionally, an intrusion alarm system operates as a standalone network of sensors designed to detect unauthorized entry into a building or perimeter. This network typically comprises door and window contacts, passive infrared (PIR) motion detectors, glass-break sensors, and a central control panel.
Historically, when an intrusion alarm was triggered, it would sound a localized siren and notify a keyholder or dispatch law enforcement. However, this legacy approach operated in a vacuum. The alarm did not “speak” to the cameras, nor did it interact with the electronic door locks. Today, the modern IP-enabled intrusion alarm operates as a smart edge device capable of continuous, two-way communication with other security infrastructure — controllable via touchscreen, keypad, or smartphone app for full remote management.
Bridging the Gap: How an Intrusion Alarm Syncs with CCTV Systems
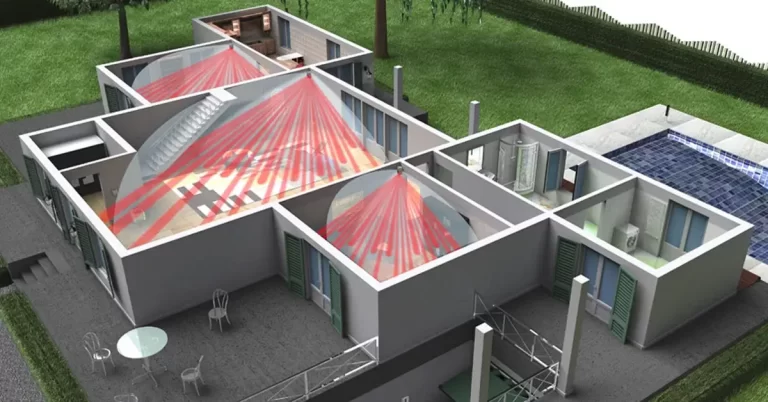
Integrating an intrusion alarm with a Video Management System (VMS) or CCTV network is arguably the most impactful upgrade a facility can make. This convergence transforms passive video recording into an active, event-driven surveillance network.
Visual Verification and Real-Time VMS Alerts
One of the primary challenges of a standalone intrusion alarm is the high rate of false alarms. Wind, wandering animals, or employee error can easily trigger a motion sensor, leading to costly police dispatch fees and alert fatigue. When integrated with CCTV, an alarm event instantly triggers visual verification. If a perimeter sensor detects movement, the VMS can automatically bring the camera covering that specific zone to the forefront of the security operator’s monitor. This allows human operators to visually confirm whether the threat is a genuine break-in or merely a stray dog, drastically reducing false alarm penalties.
Automating Pan-Tilt-Zoom (PTZ) Camera Presets
Advanced integration allows an intrusion alarm to directly control camera hardware. Consider a large industrial yard monitored by several PTZ cameras. When a fence-line intrusion sensor is breached, the alarm system sends an immediate data packet to the CCTV system. The VMS then forces the nearest PTZ camera to snap to a pre-programmed coordinate (a “preset”) directly facing the breached zone. This guarantees that critical evidence is captured from the exact moment of the intrusion, without requiring a human operator to manually aim the camera.
Seamless Synergy: Intrusion Alarms and Access Control
While video surveillance provides the “eyes” of your security operation, access control serves as the “gatekeeper.” Merging your electronic door access system with your intrusion alarm streamlines daily operations and fortifies your building against sophisticated physical attacks.
Automated Disarming and Arming via Access Credentials
In a siloed environment, the first employee to arrive at the office must unlock the front door using a keycard, quickly step inside, and punch a code into the intrusion alarm keypad before the entry delay expires. This process is prone to user error, resulting in accidental alarms. Through integration, the system recognizes the credentials of an authorized manager. When the manager swipes their smart card or mobile credential at the main entry reader, the access control system communicates with the alarm panel, instantly disarming the building. Conversely, when the last person badges out for the night, the system can automatically arm the intrusion alarm.
Dynamic Lockdown Protocols
In the event of an active threat or severe security breach, seconds matter. An integrated system allows for automated lockdown protocols. If a specific critical zone’s intrusion alarm is triggered during off-hours, the integrated system can automatically command the access control platform to lock down all exterior doors, revoke access privileges for all standard employee badges, and secure interior fire doors to trap the intruder in a specific sector.
The Tangible Benefits of a Unified Security Ecosystem
Moving from fragmented systems to a converged security dashboard provides profound operational advantages. Security teams transition from managing hardware to managing actionable intelligence.
Drastic Reduction in Response Times
By linking an intrusion alarm to live video feeds, operators eliminate the time spent cross-referencing alarm zones with camera maps. Information is centralized in a “single pane of glass.”
Mitigation of False Alarms
Visual verification ensures that emergency services are only dispatched for verified threats, saving organizations thousands of dollars in municipal fines and preserving the credibility of the site with local law enforcement.
Centralized Auditing and Compliance
For heavily regulated industries (like pharmaceuticals or finance), integrated systems generate unified audit logs. An investigator can instantly pull a report showing the moment a door was forced, the corresponding intrusion alarm event, and the associated video clip, all perfectly time-synced.
Lower Operational Complexity
Training new security personnel becomes significantly easier. Instead of mastering three distinct software interfaces, guards learn a single Physical Security Information Management (PSIM) or VMS dashboard.
Industry Perspectives on Integrated Security
Industry consensus clearly points toward integration as the future of facility management. Organizations that migrate to a unified platform featuring a synchronized intrusion alarm, access control, and VMS consistently experience faster threat resolution times compared to those using disparate systems. Enterprise security directors increasingly view API-level integration as a mandatory requirement for all new security hardware procurements, reflecting a broader shift toward holistic, converged security ecosystems.
The Integrated Security Advantage
An isolated intrusion alarm only tells you that a rule was broken. But an integrated system tells you exactly where it was broken, provides high-definition video of the event, and automatically secures the rest of the perimeter. It transforms raw data into immediate, actionable context — giving security teams the situational awareness they need to respond with confidence.
Step-by-Step Guide: Planning Your Integration Strategy
If you are ready to elevate your facility’s security by connecting your intrusion alarm to your video and access systems, following a structured deployment path is essential.
- Conduct a Comprehensive Infrastructure Audit. Begin by cataloging your existing hardware. Identify the make, model, and firmware version of your current intrusion alarm panel, NVR/VMS, and access control server.
- Choose Your Unifying Platform. You must decide which system will act as the “brain” or the primary user interface. In most modern setups, the Video Management System (VMS) or a dedicated Physical Security Information Management (PSIM) software acts as the central hub, pulling in data from the intrusion alarm and access control modules.
- Engage Certified Security Integrators. Integration is rarely a plug-and-play endeavor. Partner with certified security integrators who have proven experience with the specific brands of hardware you are utilizing. They will ensure that data flows securely between devices without compromising the standalone reliability of the intrusion alarm.
- Establish Logic Rules and Test Vigorously. Define exactly what the CCTV system should do when an alarm sounds in the server room versus the lobby. Once configured, conduct rigorous penetration and scenario testing to ensure the integration performs flawlessly under stress.
Conclusion: Future-Proofing with a Connected Intrusion Alarm
The days of relying on isolated security devices are rapidly coming to an end. Answering the question, “Can an intrusion alarm integrate with existing CCTV and access control systems?” requires looking beyond simple technical feasibility. It requires recognizing that integration is a strategic imperative.
By effectively syncing your intrusion alarm with intelligent video surveillance and dynamic access control protocols, you create an impenetrable, automated security ecosystem. This unified approach not only drastically improves incident response times and mitigates false alarms but also provides security personnel with unparalleled situational awareness. As technology continues to advance, investing in an integrated framework ensures that your physical security infrastructure remains robust, adaptable, and prepared for whatever threats tomorrow may bring.